BENCHMARK YOUR EXTERNAL INFRASTRUCTURE
EXTERNAL PENETRATION TESTING
External Penetration Testing involves simulating cyber-attacks from an outside perspective to target an organization’s public-facing systems such as websites, email servers, and external network services. The primary objective is to identify and exploit vulnerabilities, thereby enabling organizations to gain a more comprehensive understanding of the threats, risks, and impacts they face, and to proactively improve their cybersecurity defenses.
Tell us
about your scope
What You'll Get

Key findings, risks, impacts, and critical recommendations.

Overview of methodologies, standards, tactics, and techniques used.

Detailed vulnerability analysis, reproduction steps, PoC, evidence.

Strategic and tactical walkthrough on how to fix vulnerabilities.

Comprehensive advice on cybersecurity enhancement strategies.

Offered once vulnerabilities are fixed.
What is External Penetration Testing?
The network edge is the last barrier to the open internet. With increased data breaches and attacks on businesses of all sizes, customers, regulators, and insurers require external penetration testing to ensure the perimeter is a reliable stronghold against attackers. At Secragon, we specialize in penetration tests that are 95% manual, designed to replicate real-world hacking, and conducted by experienced ethical hackers. Along with leveraging industry standard methodologies to ensure a thorough security assessment is conducted under safe and controlled conditions, our expert team utilizes an advanced mix of public and in-house developed exploits and in-depth analysis to discover vulnerabilities not yet published and often not yet discovered. The objective is to penetrate target systems and evaluate the robustness of the external network’s security so that the organization can implement protective measures to mitigate risk.
Our service not only identifies security gaps but also provides a prioritized action plan with remediation guidance to help you address any risks found. We don’t just point out security holes; we help you solve them.

Gain in-depth awareness of your external risk profile, providing crucial intelligence for managerial decision-making in cybersecurity.
Test the investments you have made in your cybersecurity tools and technology to determine if any vulnerabilities or gaps exist and whether they can stop a sophisticated attack on your organization.
Many industries require regular external penetration testing for compliance with sector-specific regulations or standards. By conducting these tests, you can demonstrate your commitment to cybersecurity, avoid potential penalties, and maintain the trust of clients and stakeholders.
An external pen test prevents brand reputation damage and financial impacts by proactively finding flaws before hackers potentially exploit them in an actual breach scenario.
As remote working becomes more prevalent, external penetration testing is increasingly important for securing VPNs, personal devices, and other remote access points. Regular testing ensures that your employees can work safely from any location, protecting your business and staff from cyber threats.
Why Conduct an External Pentest?
Holes in your system could lead to data breaches, service outages, reputational damage, and regulatory penalties. Conducting an external penetration test provides invaluable insights into the potential security risks your organization may face from external threats. Here is what your organization will gain after conducting a project with our team:
PROTECT AGAINST THE LATEST THREATS
When Should You Perform an External Penetration Test?
External penetration testing should be conducted regularly to identify and address vulnerabilities inadvertently introduced in public-facing systems and reduce the risk of cyber attacks. It’s important to note that the frequency and timing can vary depending on the organization’s size, the complexity of the network, and the sensitivity of the data handled. Here are key instances when they should be performed:
Significant Updates
After implementing substantial changes or upgrades to your external network infrastructure or platforms.
New Services
Prior to the official launch of new public-facing services, applications, or web functionalities.
Regulatory Compliance
To ensure adherence to necessary external compliance and regulatory standards specific to your industry.
Post-Security Incident
Following the investigation and remediation of any security breaches or exposures to external threats.
Annually
As part of a strategic, scheduled plan to proactively detect and mitigate external vulnerabilities.
Public Interface Overhauls
After any significant redesigns, updates, or changes to websites, portals, or other public-facing digital assets.
We Provide Expert Solutions And Definite Results

Transparent
Pricing
Clear, upfront, with no
hidden costs.

Dedicated Project
Manager
Your security is our
commitment.

Retesting After
Fixes
Ensuring threats are
truly eliminated.

Affordable
Expertise
Premium protection,
reasonable rates.

Customized
Approach
Solutions fitted to your
specific needs.

Proactive
Protection
Effectively securing your
digital assets.
What Will be Assessed During an External Penetration Test?
An external penetration test identifies vulnerabilities in your Internet-facing IT systems and external network perimeter systems, including:
Security Perimeter
Firewalls, IDS/IPS, VPNs, network devices and configurations.
Remote Access
Remote access services, protocols and applications like RDP, SSH, Citrix, Terminal Services, associated access controls.
Web Infrastructure
Web servers, web applications, frameworks, plugins, associated vulnerabilities.
Domain Evaluation
DNS servers, records, domain registration details, DNSSEC, IPv6 implementations,
Email Systems
Mail servers, mail protocols,
antispam/antivirus controls, email authentication mechanisms (DKIM, DMARC, SPF), etc.
And More
Including Dark Web leaks, SSL/TLS configurations, third-party integrations, default credentials checks, etc.
Our Penetration Testing Process
If your organization has not gone through a penetration test before, you may not know what to expect. Even if you have, maybe you are wondering what Secragon’s stages of penetration testing are. Here is a high-level break down of each step of our proven process:

Activities: Engage stakeholders, define targets, plan logistics for efficient, transparent execution.
Outcomes: Scope Validation, Proposal, Contract.
Activities: Environment preparation, OSINT collection, attack scenario planning.
Outcomes: Strategy Development, Threat Insight.
Activities: Vulnerability identification, active exploitation, privilege escalation, execution of realistic attack scenarios, data and information collection, persistence maintenance, and documentation of steps.
Outcomes: Comprehensive Report, including Executive Summary, Technical Details, Impact Analysis, Recommendations.
Activities: Supporting vulnerability remediation with actionable steps and advice, answering follow-up queries.
Outcomes: Remediation Plan, Security Enhancement.
Activities: Validate the effectiveness of remediation efforts through complementary retesting.
Outcomes: Re-test Results, Attestation.
Frequently Asked Questions
Couldn’t find the information you were looking for?
Internal pentesting is conducted from within the organization’s network by a tester who has access to the internal network. External pentesting is conducted from outside the organization’s network and simulates an attack on public-facing systems. The primary difference is the point of origin of the test, with internal testing being more focused on internal network security measures while external testing focuses on identifying vulnerabilities in systems that are accessible from the internet.
When determining the scope of a penetration test, it’s essential to tailor it to the business’s unique characteristics and risk profile, considering factors such as the nature of the business, products/services offered, compliance requirements, geographic factors, organizational structure, strategic plans, stakeholder expectations (especially regarding customer data custody), asset value, network segmentation, connectivity, the age of the environment’s components, and any recent or planned changes. Understanding these elements ensures that the test is appropriately focused and effective in addressing the most relevant areas of the environment.
We typically are able to schedule out within 5-10 days from a scoping call. Chat with us today if you require an urgent test. We’re here to help!
In general, there is no need for anything special to prepare for a penetration test with respect to how security controls are managed on a day-to-day basis. An organization should expect to participate in preparation activities related to planning the penetration test itself to ensure the test is performed under controlled conditions.
The hiring company should be prepared to have documentation available that details the in-scope IP ranges and also be ready to prepare test environments.
Client data protection is our priority. We use non-destructive methods during our assessments and maintain strict confidentiality.
External penetration testing is a critical component of any comprehensive cybersecurity strategy. By identifying vulnerabilities and weaknesses in your external infrastructure, you can take proactive steps to protect your organization from the most likely risks of facing potential attacks. Regular testing can help ensure that your security measures are up-to-date and effective, and can provide valuable insights into areas that may require additional attention or investment.
Download The
Secragon External Penetration Testing Sample Report!
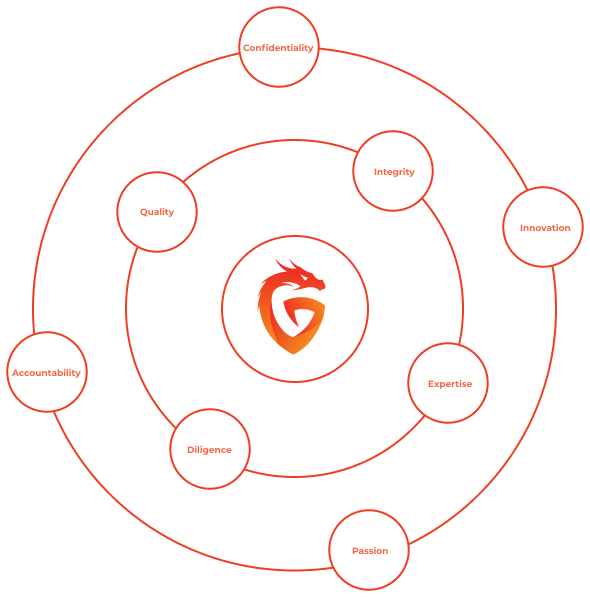
SECRAGON, YOUR CYBERSECURITY PROVIDER
We, at Secragon, are a team of certified ethical hackers, visionary security engineers, seasoned penetration testers, and committed project managers… but first of all – professionals, who LIVE and BREATHE Offensive Security. Along the list of qualifications, titles, and credentials, we bring a real “think outside of the box” mindset to every project and we constantly strive to learn, explore, and push forward to master complex concepts and deliver top-notch services and results.


